Being in a digital world means that everything people use involves technology, and each technology comes with some risk. Digital accounts today store our most important information, including everything from bank details to our private photos. As important as these things are to us, hackers continually target these valuable collections of information. Additionally, over 300,000 phishing attacks occur every day. Cybercriminals use sophisticated tactics to steal your accounts without your knowledge. This blog explains common hacking techniques and provides important security information to keep you safe. So, let’s begin!
Common Tactics Hackers Use
Hackers use various tricks to gain unauthorized access to your accounts. They begin by discovering security weaknesses in your digital activities. The following tactics are commonly used by hackers.
1. Phishing
- Phishing is the most common method hackers use to conduct attacks.
- Hackers use fake emails and messages that imitate authentic communications from banks and popular applications.
- The messages ask you to click a link and enter your login information.
- Hackers immediately obtain your login information as soon as you enter it.
2. Malware
- Malware is a common tool used in hacking activities.
- Hackers use infected downloads, attachments, and compromised websites to distribute viruses or spyware.
- The software runs in the background on your device, collecting your personal information while stealing your passwords.
- Keyloggers record all your keystrokes, exposing your private information
- Ransomware prevents you from accessing your files until you pay a ransom.
- This typically occurs after hackers have already extracted all your data.
3. Brute Force Attacks
- Brute force attacks occur when hackers use automated tools to guess passwords.
- The process becomes easier when users use weak passwords such as ‘123456’ and ‘password.
4. Social Engineering
- Social engineering relies on human interaction.
- Hackers use social media and phone calls to impersonate friends and support staff members.
- They trick you into sharing personal information and giving them access to your accounts.
5. Man-in-the-Middle Attacks
- Man-in-the-middle attacks capture data as it travels between two parties.
- Unsecured Wi-Fi networks serve as one example of a situation where interception occurs.
- This enables hackers to listen to your private conversations.
How to Protect Your Accounts
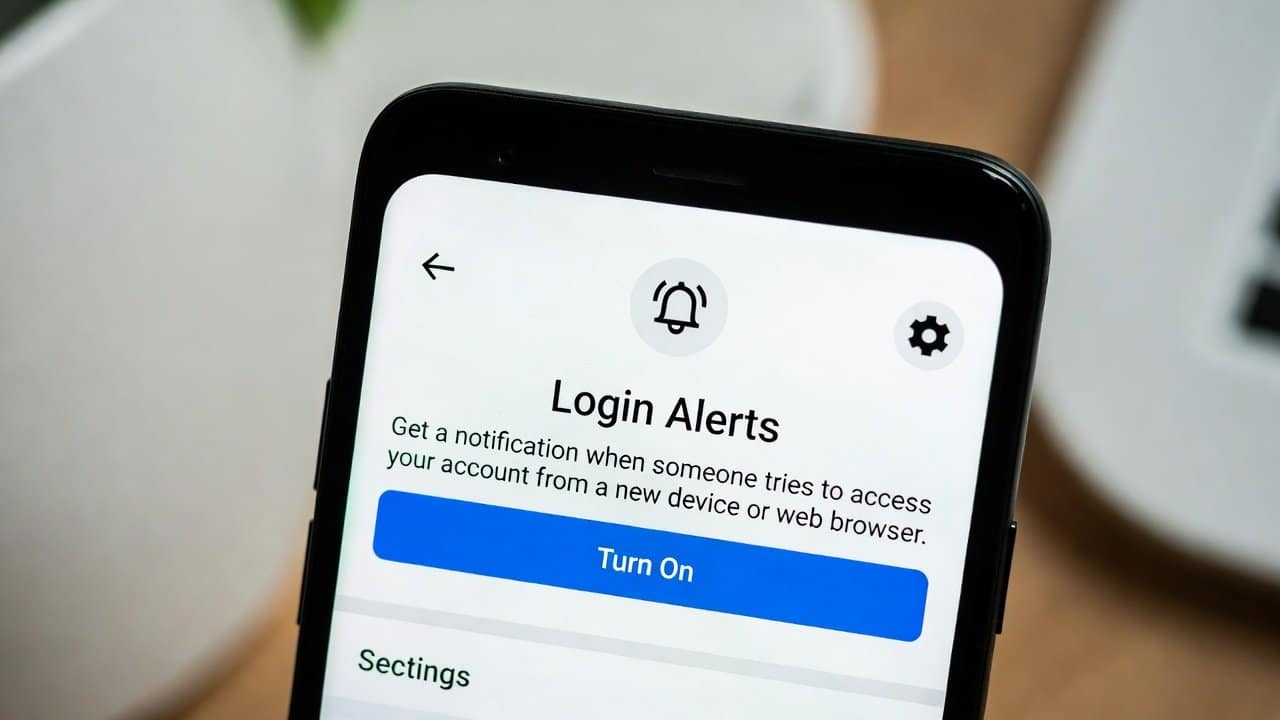
- All users must activate two-factor authentication (2FA).
- Two-factor authentication requires users to enter security codes sent to their mobile devices or authentication applications.
- Users must create strong, unique passwords for each website and use a password manager to store them.
- Also, they should maintain the ability to identify suspicious links by checking their URLs before deciding to click.
- Users need to update their software and devices regularly to eliminate security weaknesses.
- Users should avoid public Wi-Fi networks when performing sensitive activities and use a VPN to protect their online connections.
- Users and their families must learn about phishing scams to identify them and verify all information.
Conclusion
In the end, hackers develop new techniques to attack systems. Organizations need to create security measures that will evolve to fight these attacks. Your online protection needs to identify phishing attempts, detect malware, enforce strong password security, and promote secure online behavior. Furthermore, your awareness of the danger of a single click to your safety will help you establish control over your digital security. You should take steps to protect your accounts now, because your future self will appreciate your decision.